A newly documented ransomware strain called VECT 2.0 has alarmed the cybersecurity community for a reason that sets it apart from virtually all other ransomware families: a critical coding flaw in its encryption logic that permanently destroys any file larger than 128 KB, rendering recovery impossible even if victims pay the ransom.
Origins and Rapid Expansion
VECT Ransomware first appeared in December 2025 on a Russian-language cybercrime forum, where it was launched as a Ransomware-as-a-Service (RaaS) program. The group claimed its first two victims in January 2026 and released version 2.0 in February 2026, expanding its targeting scope across Windows, Linux, and VMware ESXi environments.
The malware gained significant visibility in March 2026 when VECT announced a partnership with TeamPCP, a threat actor responsible for supply-chain attacks that had previously injected malware into widely-used open-source packages including Trivy, Checkmarx KICS, LiteLLM, and Telnyx. This partnership exponentially increased VECT’s potential distribution reach.
Open-Affiliate Model Lowers the Bar
Check Point Research analysts obtained access to VECT 2.0’s builder panel through a BreachForums account and conducted a thorough technical analysis of all three platform variants. Their investigation revealed that VECT entered a partnership with BreachForums itself, giving every registered forum member free access to deploy the ransomware as an affiliate — with no vetting process required.
This open-affiliate model represents a significant escalation in the ransomware-as-a-service ecosystem. By removing the standard qualification requirements for affiliates, VECT dramatically lowers the technical barrier for less experienced attackers to participate in ransomware operations, effectively crowdsourcing its attack capability.
The Technical Architecture
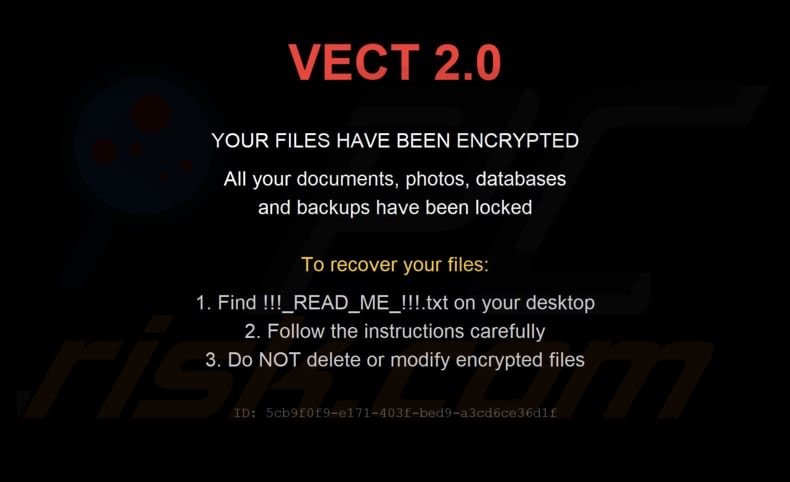
VECT 2.0 is written in C++ and targets all three platforms through statically compiled executables that share a common codebase. Each variant uses the ChaCha20-IETF (RFC 8439) cipher via the libsodium cryptographic library and renames encrypted files with the .vect extension, dropping a ransom note named !!!READ_ME!!!.txt on each compromised system.
The Fatal Flaw: Files Over 128 KB Are Permanently Destroyed
The most alarming aspect of VECT 2.0 is a fundamental error in its encryption implementation that turns the ransomware into an effective data wiper. Any file exceeding 131,072 bytes (128 KB) is not properly encrypted — it is rendered permanently unrecoverable. This means the very assets organizations depend on most — databases, virtual machine images, backups, and large documents — are simply destroyed rather than held for ransom.
At the root of the problem is a critical error in how VECT 2.0 handles cryptographic nonces during the encryption of large files. When processing files above the threshold, the malware divides them into four chunks and encrypts each with a freshly generated, random 12-byte nonce. Due to a flaw in how these nonces are written and tracked, the original file data cannot be recovered even with the correct decryption key. The decryption process simply fails, and the file data is lost permanently.
Multi-Platform Targeting
The availability of VECT 2.0 variants for Windows, Linux, and VMware ESXi makes it a particularly dangerous threat to enterprise environments. The ESXi variant is especially concerning because it can target entire virtualized infrastructure stacks — encrypting (and in most cases destroying) the virtual disk files that power an organization’s servers, potentially taking down entire data centers in a single attack.
Implications for Incident Response
The destructive nature of VECT 2.0’s encryption flaw fundamentally changes the calculus for incident response teams. In a standard ransomware attack, paying the ransom — while generally discouraged — at least offers the possibility of file recovery. With VECT 2.0, any file over 128 KB processed by the malware is simply gone, whether the ransom is paid or not. This makes robust, tested, offline backups the only viable recovery option.
Defensive Recommendations
- Maintain offline backups of all critical data, stored in a location completely isolated from the primary network.
- Test backup restoration procedures regularly to ensure recovery is possible in the event of a ransomware attack.
- Monitor for VECT indicators of compromise: Look for the
.vectfile extension and ransom notes named!!!READ_ME!!!.txt. - Audit affiliate access to cybercrime platforms: The open-affiliate model means VECT may be deployed by attackers with limited sophistication — expand threat detection to account for less technically capable adversaries.
- Patch and secure ESXi environments as a priority, given the availability of an ESXi-targeting variant.
VECT 2.0 represents a new category of threat: ransomware that destroys data not by design, but through incompetence. The result for victims is the same — permanent, irrecoverable data loss — making prevention and offline backups the only reliable defense.