In the dynamic and ever-evolving landscape of cyber threats, a new malevolent force has emerged, casting a foreboding shadow over the digital realm—Mallox ransomware. With its first appearance in 2021, Mallox, also known as TargetCompany, has swiftly risen to prominence as a formidable adversary in the dark world of ransomware. In this comprehensive analysis, we delve into the latest activities of Mallox, shedding light on its methods of operation, preferred entry points, and the intricacies of its menacing payloads.
Operating under the Ransomware-as-a-Service (RaaS) model, Mallox exhibits a level of sophistication that sets it apart. The group strategically leverages underground forums like Nulled and RAMP to advertise and expand its nefarious services. With a dedicated TOR-based leak site and a prominent presence on social media platforms, including Twitter/X, Mallox boldly publicizes its conquests and exposes stolen enterprise data, creating a chilling narrative of cyber threats.
The core of Mallox’s modus operandi revolves around exploiting vulnerabilities in publicly exposed services, with a keen focus on MS-SQL (Microsoft SQL Server) and ODBC interfaces. The group targets specific unpatched remote code execution vulnerabilities, such as CVE-2019-1068 and CVE-2020-0618 in Microsoft SQL Server, showcasing a high level of technical prowess. Additionally, Mallox employs brute-force attacks against weakly configured services, gaining initial access through dictionary-based assaults on MS-SQL interfaces.
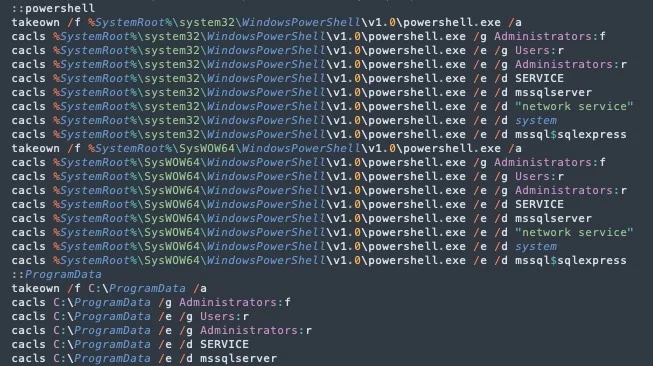
Once inside a system, Mallox’s actors act swiftly, executing PowerShell commands to run various batch scripts and download the ransomware payload. Tools like Kill-Delete.bat and Bwmeldokiller.bat are strategically used to eliminate obstacles to the encryption routine. The ransomware payload, known as “Mallox.Resurrection,” showcases the group’s adaptability and persistence, featuring hard-coded exclusions that spare specific file types and processes from encryption. This meticulous and selective approach highlights the refinement and strategic nature of Mallox’s operations, ensuring maximum impact with minimal collateral damage.
For those unfortunate enough to fall victim to Mallox, non-compliance with ransom demands poses a grave threat—the exposure of their data on the group’s data leak site. This pressure tactic underscores the urgency for robust cybersecurity measures. Despite setbacks, such as the release of a public decryptor for earlier versions of its payloads, Mallox remains resilient, continuously exploiting unpatched MS-SQL interfaces and weak passwords.
In conclusion, the relentless evolution of Mallox ransomware serves as a stark reminder of the ever-present danger in the cyber world. It is a clarion call for organizations and individuals to remain vigilant, update regularly, and invest in advanced cybersecurity defenses to ward off the insidious threats posed by adversaries like Mallox. As the digital battleground continues to evolve, the imperative to fortify our defenses against such sophisticated and persistent threats has never been more critical.